AI-based cyber security Tools equip businesses with an advanced toolkit to counter the persistent threat of cyberattacks. From identifying suspicious patterns to proactive threat hunting, these solutions offer a proactive and intelligent defense mechanism against malicious activities.
The urgency for AI in security solutions is evident as cybercriminals continually evolve their techniques to breach security systems and compromise sensitive data. Relying solely on traditional cybersecurity solutions may prove inadequate in thwarting these attacks, making AI support more crucial than ever.
We conducted a comprehensive review of 20 top-rated AI security solutions, analyzing their features, pricing, as well as pros and cons. Additionally, we have compiled a list of 20 honorable mentions to assist you in selecting the most suitable AI security tool for your business.
Top AI Security Software: Comparison Chart
Here is a head-to-head feature summary comparison of the top-rated AI security software.
| Best for | Behavioral analysis | Complexity | Starting price | |
|---|---|---|---|---|
| Darktrace | Neutralizing novel threats | Yes | High | $30,000 |
| CrowdStrike | Monitoring user endpoint behavior | Yes | High | $299.95 per year |
| SentinelOne | Advanced threat-hunting and incident response capabilities | Yes | Low | $69.99 per endpoint |
| Check Point Software | Network monitoring and security | Yes | High | Available upon request |
| Fortinet | Preventing zero-day threats | Yes | High | Available upon request |
| Zscaler | Data loss prevention | Yes | Moderate | Available upon request |
| Trellix | Complex IT environments that require continuous monitoring | Yes | High | Available upon request |
| Vectra AI | Hybrid attack detection, investigation, and response | Yes | Moderate | $4 per month per IP |
| Cybereason | Defending against MalOps | Yes | High | Available upon request |
| Tessian | Protecting against email-based threats | Yes | High | $40,080 per year |
![]()
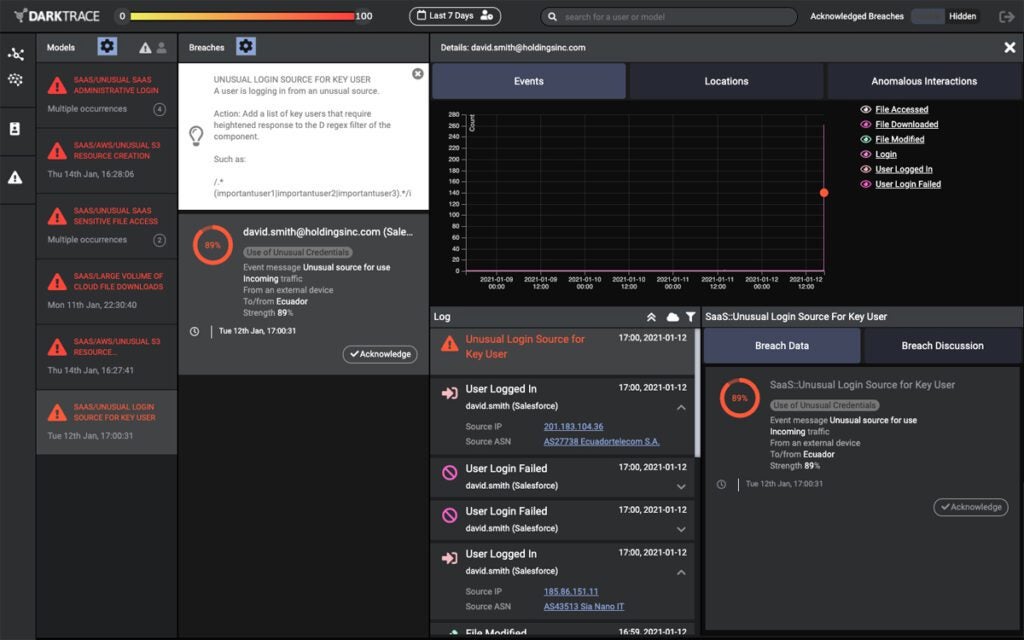
Darktrace: Best for Handling Novel Threats
Darktrace’s cyber AI platform uses AI and ML algorithms to identify and respond to cyberthreats in real time. The platform offers a unified solution that provides protection across the cloud, SaaS, email, IoT, ICS, remote endpoints, and the network.
Darktrace’s self-learning AI technology is designed to understand and adapt to the unique patterns of a company’s network by learning from users and devices as well as the connections between them, allowing it to detect anomalous, novel behavior that may indicate a cyberattack.
The platform offers various AI-supported services, such as AI-based attack simulation and AI incident investigation and reporting. Darktrace’s AI algorithms constantly learn and adapt to the evolving threat landscape, enabling it to identify known and unknown threats and detect abnormal activity that may indicate the presence of previously unseen threats.
To that end, Darktrace is geared to combat LOTL (living off the land) attacks, highly targeted attacks and – increasingly important – AI attacks.
Pros and Cons
| Pros | Cons |
|---|---|
| Hardens defenses. | Users say the tool is pricey, especially for small businesses. |
| Instant visibility of attacks. | Complex initial setup. |
| Empowers security teams with autonomous, always-on, AI-driven capabilities. | |
| Responsive and quality technical support. |
Pricing
Darktrace doesn’t advertise its product pricing on its websites. Publicly available data shows the platform has a 30-day free trial for proof of value.
- Small bandwidth with up to 300 Mbps of average bandwidth and 200 hosts: Costs $30,000.
- Medium bandwidth with up to 2 Gbps of average bandwidth and 1,000 hosts: Costs $60,000.
- Large bandwidth with up to 5 Gbps of average bandwidth and 10,000 hosts: Costs $100,000.
For your actual pricing, contact the company for a custom quote.
Features
- Darktrace PREVENT – continuously monitors your attack surface for risks, high-impact vulnerabilities, and external threats.
- Darktrace DETECT – offers instant visibility of threats.
- Darktrace RESPOND – capable of interrupting fast-moving attacks and is customizable to take action only at specific times, on certain devices, or in response to certain events.
- Darktrace HEAL – restore your system back to health after an attack.
For a deeper understanding of cybersecurity and AI, read our guide: Generative AI and Cybersecurity
![]()
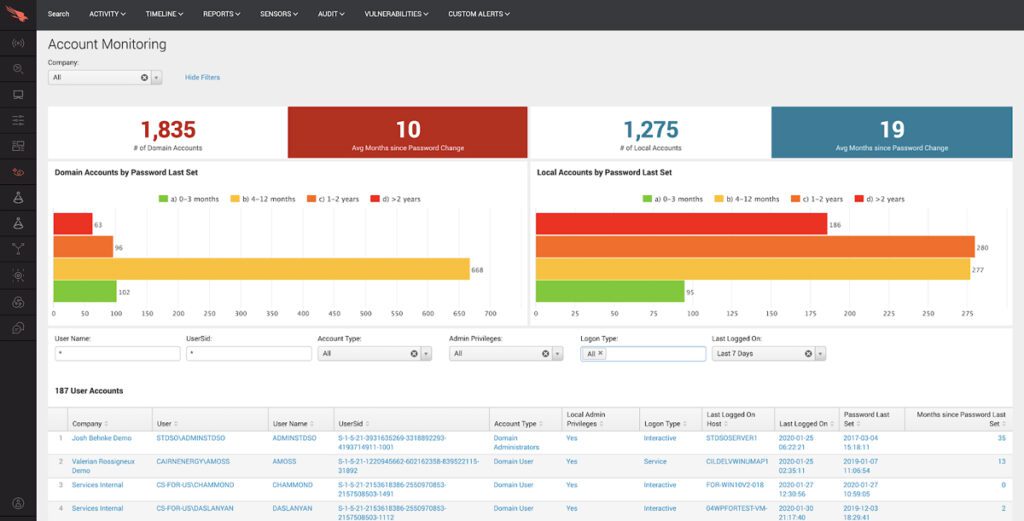
CrowdStrike: Best for Monitoring User Endpoint Behavior
The CrowdStrike Falcon is an AI-native security solution that leverages machine learning, behavioral AI, and a custom large language model to protect endpoints, detect threats, and respond to security incidents in real time. It consolidates next-generation antivirus (AV), endpoint detection and response (EDR), and a 24/7 managed hunting service into a single lightweight agent, providing organizations with complete visibility and protection across their endpoints.
The lightweight agent continuously monitors and protects endpoints against various attacks by leveraging real-time indicators of attack and threat intelligence from across the enterprise, thereby providing proactive threat-hunting capabilities.
CrowdStrike uses behavioral AI to detect anomalies in user endpoint behavior, meaning it can monitor current activity as compared with past user actions to protect the perimeter. Its models are trained on trillions of data points daily, allowing it to target threats ahead of time.
Pros and Cons
| Pros | Cons |
|---|---|
| Provides visibility across devices, users, accounts, applications, and cloud workloads. | The user interface can be improved. |
| Can stop identity-based attacks in real-time. | Requires time investment for users to get familiar with the platform’s capabilities. |
| Real-time insights with automated threat intelligence. | |
| The platform is highly modular and extensible. |
Pricing
All bundles require a minimum purchase of 5 devices.
- Falcon Go: $299.95 per year.
- Falcon Pro: $499.95 per year.
- Falcon Enterprise: $924.95 per year.
- Falcon Elite: Custom pricing.
- Falcon Complete MDR: Pricing is available upon request.
Features
- Unified attack surface visibility.
- Pre- and post-incident response services.
- Supports importing IOCs.
- Uses an AI-based detection system called user and entity behavior analytics (UEBA).
![]()
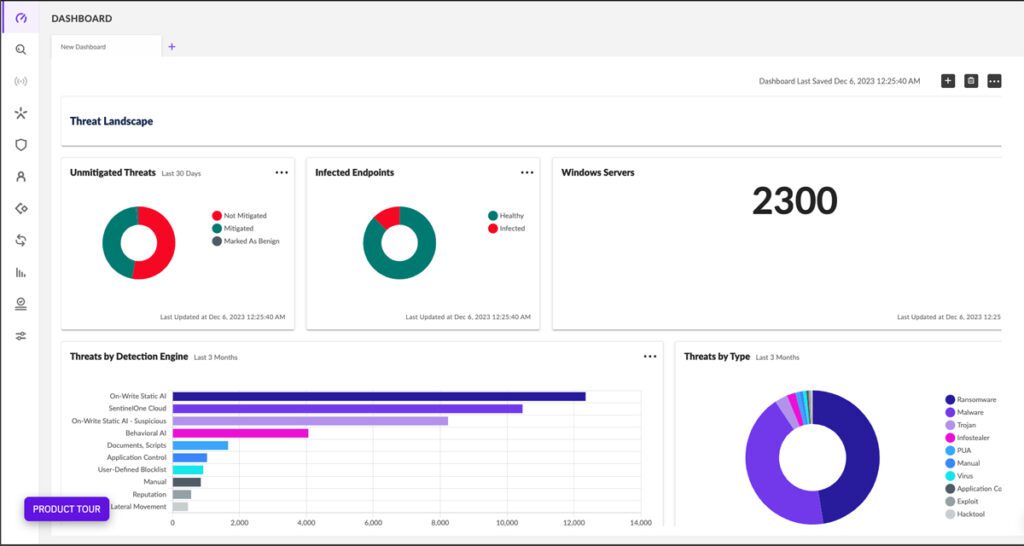
SentinelOne: Best for Advanced Threat-Hunting and Incident Response Capabilities
SentinelOne’s AI-backed cybersecurity solution, SentinelOne Singularity, is an autonomous security platform that combines endpoint protection platform (EPP), EDR, and extended detection and response (XDR) into a single unified platform.
The platform leverages AI and ML algorithms to provide real-time prevention, detection, response, and threat hunting across user endpoints, containers, cloud workloads, and IoT devices. It protects against a wide array of cyberthreats, including malware, ransomware, exploits, and fileless attacks.
We ranked SentinelOne’s Singularity as one of the best AI security solutions because it aims to simplify and strengthen enterprise security operations by providing comprehensive and automated protection across the entire threat lifecycle, from pre-execution to post-execution.
In sum, its integrated suite of tools works in concert to enable excellent incident response and threat hunting functionality.
Pros and Cons
| Pros | Cons |
|---|---|
| Provides quality threat-hunting tools and insights. | Digital forensics and incident response are only available to enterprise users. |
| 24/7/365 threat hunting and managed services. | The platform’s reporting capability could be better. |
| Easy to deploy. |
Pricing
- Singularity Core: $69.99 per endpoint.
- Singularity Control: $79.99 per endpoint.
- Singularity Complete: $159.99 per endpoint.
- Singularity Commercial: $209.99 per endpoint.
- Singularity Enterprise: Pricing is available upon request.
Features
- Ability to identify and triage threats.
- Enables companies to ingest data from various sources.
- Identifying and then very quickly launch threat detection and response.
- Advanced threat-hunting capabilities.
![]()
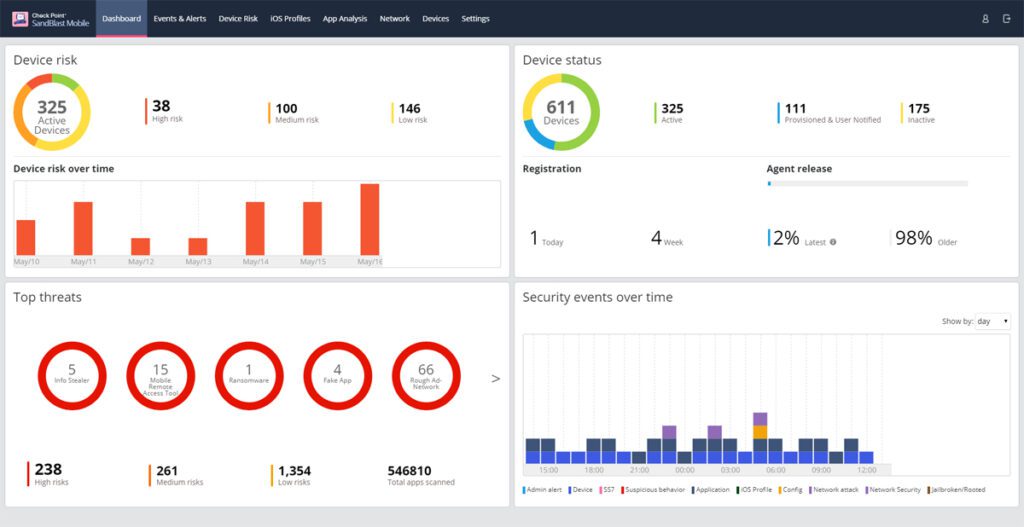
Check Point Software: Best for Network Monitoring and Security
Check Point Software Technologies leverages AI capabilities to enhance its cybersecurity offerings at various levels. Its ThreatCloud AI platform, which drives the actions of the platform’s elements, collects and analyzes threat data from various sources.
This AI intelligence also supports Check Point’s global sensors, research teams, customers, and partner community. This intelligence is then integrated into Check Point’s security solutions to protect against known and unknown threats – the AI enables the response to be proactive.
Check Point’s Quantum also leverages AI and deep learning capabilities to protect your network, cloud, data center, IoT, and remote users against Gen V cyberattacks (also known as “advanced weapon grade” attacks). Its threat prevention solution includes security features such as a firewall, intrusion prevention system (IPS), anti-bot, antivirus, application control, and URL filtering to enable you to combat cyberattacks and threats.
Pros and Cons
| Pros | Cons |
|---|---|
| XDR/XPR incidents aggregation. | Some users may find Check Point’s services to be expensive. |
| Improves accuracy with network AI and mobile AI engines aggregator as well as machine-validated signature. | Steep learning curve. |
| Exposes stealth breaches. |
Pricing
Check Point doesn’t advertise its rates on its websites. Contact the company for a detailed quote.
Features
- Prevent known and zero-day attacks across networks, endpoints, cloud, and email.
- Uses UEBA to identify anomalous behavior indicative of a potential threat.
- Third-party threat intelligence feeds.
- ThreatCloud AI campaign hunting.
- Anti-phishing AI engine.
![]()
Fortinet: Best for Preventing Zero-Day Threats
Fortinet FortiGuard is an AI-powered system incorporating threat intelligence, real-time threat analysis, and global threat protection to identify and block advanced threats and attacks. The services integrate with security solutions across Fortinet’s broad portfolio to provide security capabilities that protect applications, web traffic, content, devices, and users located anywhere.
A core element: the platform is regularly updated with the latest threat intelligence from FortiGuard Labs experts, data from across Fortinet’s broad sensor base, and zero-day intelligence feeds. This ensures that organizations are protected against emerging threats and zero-day vulnerabilities.
Additionally, FortiGuard’s service portfolio includes content security and NOC/SOC security (very important given the core nature of the Security Operations Center). It also offers SOC-as-a-Service functionality and provides consistent cybersecurity assessments and readiness alerts.
Pros and Cons
| Pros | Cons |
|---|---|
| Protect against network- and file-based threats. | Steep learning curve. |
| Security profile customization. | Customer support can be better. |
| Feature-rich. |

Pricing
Fortinet doesn’t advertise its rates on its websites. Contact the company for a detailed quote.
Features
- It protects against all OWASP Top-10 threats, DDOS attacks, and bot attacks.
- Indicator of compromise detection.
- AI-based inline malware prevention.
- AI-powered SandBox engine.
- Focused on preventing zero-day threats.
![]()
Zscaler: Best for Data Loss Prevention
Zscaler is a cloud-based security platform that provides internet security and web filtering services. It uses proprietary large language models and AI to enhance and improve its security offerings.
The company’s LLMs are integrated with a massive data lake that handles more than 300 billion daily transactions, allowing for continuous learning and improvement of its AI models. This enables Zscaler to provide advanced AI-driven outcomes and capabilities for IT and security teams.
These AI-driven outcomes are particularly notable for data loss prevention; Zscaler’s common DLP use cases includes securing data in motion, securing endpoint data, and the ability to protect against misconfigurations.
Zscaler operates on the principle of zero-trust connectivity, meaning that it assumes everything on the network is potentially malicious and does not automatically trust any user or device. Instead, it authenticates and validates every user and device before granting access to resources, which also supports DLP.
Pros and Cons
| Pros | Cons |
|---|---|
| AI-powered browser isolation. | Customer support could be improved. |
| Dynamic, risk-based policy. | Requires fast internet service to function well. |
| Advanced data classification. | |
| Inline web protection. |
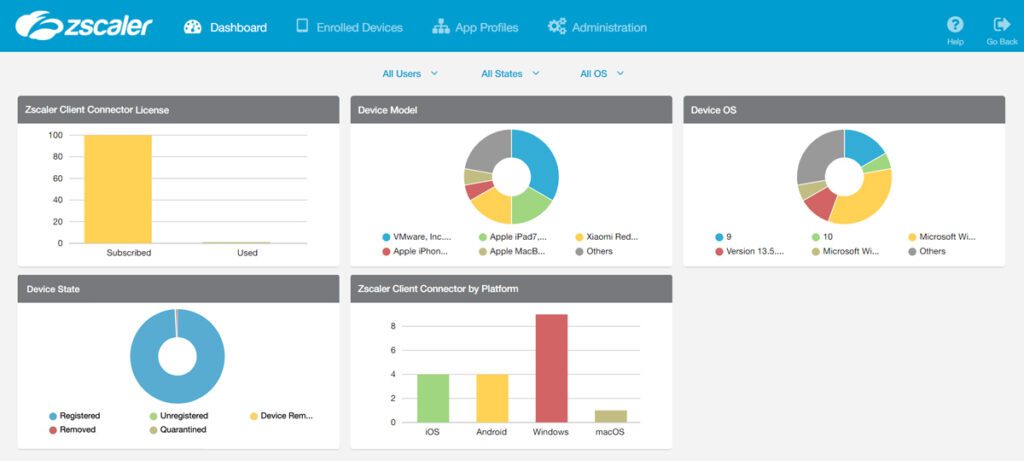
Pricing
Zscaler doesn’t advertise its rates on its websites. Contact the company for a detailed quote.
Features
- AI-powered phishing and C2 detection.
- Standard digital experience monitoring.
- Data loss prevention capability.
- AI-powered phishing detection.
- Automated, AI-powered root cause analysis.
![]()
Trellix: Best for Complex IT Environments That Require Continuous Monitoring
Trellix is a product of the merger of the security product divisions of McAfee Enterprise and FireEye. The platform excels in continuous monitoring – which enables proactive threat detection – by combining signature-based identification, behavioral analytics, and real-time monitoring.
Trellix XDR leverages advanced machine learning and AI techniques to analyze, correlate and monitor data from various sources, including network traffic, endpoint behavior and threat intelligence feeds. Its continuous monitoring enables it to detect sophisticated and complex threats that traditional security solutions might miss.
Trellix’s AI and security operation is capable of operationalizing threat intelligence, reducing alert noise and automating responses to security incidents, resulting in faster response times and proper incident management.
Notably, its XConsole combines security controls and an advanced research center to provide a unified view of the security landscape and enhanced visibility into network traffic, endpoint activity, and user behavior — allowing analysts to identify and remediate threats before they can cause damage.
Pros and Cons
| Pros | Cons |
|---|---|
| Integrates with 1,000+ third-party sources. | Complex initial setup. |
| Comprehensive on-premises product portfolio. | The user interface can be better. |
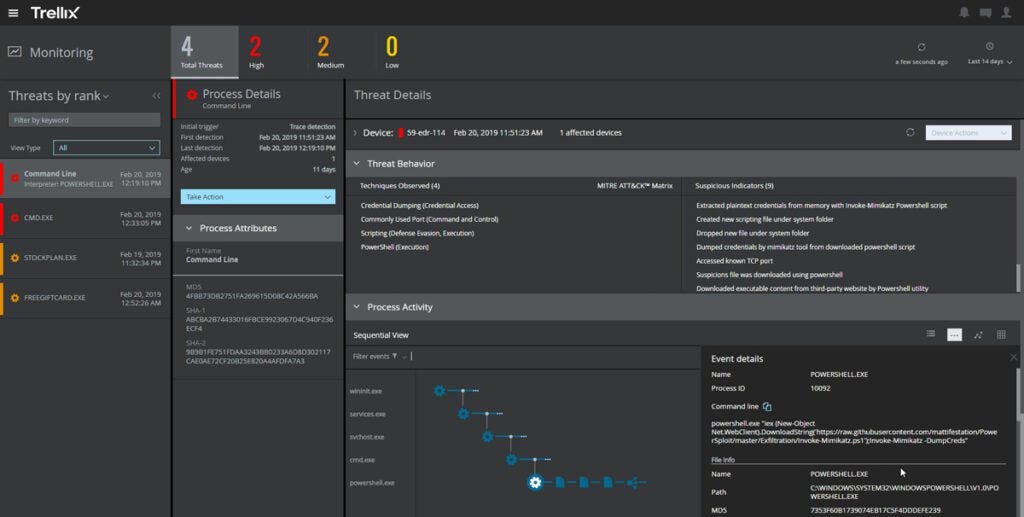
Pricing
Potential customers must contact an expert at Trellix to receive pricing information.
Features
- Signature-based engine to find and block known malware.
- Behavior-based analytics engine to stop advanced threats.
- Incorporates UEBA capabilities to detect anomalous user behaviors that may indicate insider threats or compromised accounts.
- Real-time monitoring.
![]()
Vectra AI: Best for Hybrid Attack Detection, Investigation, and Response
Vectra AI Attack Signal Intelligence platform combines human intelligence, data science, and machine learning to detect cyberattacks in real time. The company’s AI and cybersecurity solution gives organizations constant visibility into their network security posture, helps prioritize potential threats, and enables quick response and mitigation to minimize the impact of hybrid cyberattacks.
Significantly, with the prevalence of “hybrid attacks” (two or more combined attacks to break the perimeter) Vectra offers a tool to prevent these attacks. The tool combats various hybrid attack types, such as account takeovers, data breaches, ransomware, supply chain attacks, and nation state attacks – this last attack tends to be particularly robust.
Vectra AI uses the detect, prioritize, investigate, and respond model to remediate and mitigate cyberthreats and also integrates detections across identity, public cloud, SaaS, and data center networks to provide a holistic view of an organization’s security landscape.
Pros and Cons
| Pros | Cons |
|---|---|
| Attack prioritization. | Reporting capability can be improved. |
| AI-driven insights. | Product documentation can be improved. |
| Detects attacks in real time with behavior-based threat detection. |
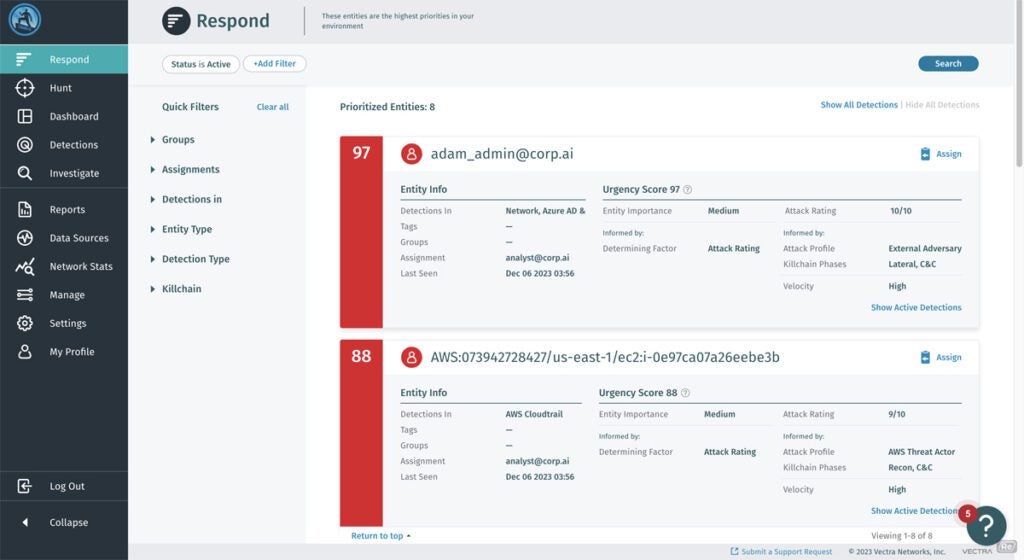
Pricing
Though Vectra AI doesn’t display product pricing on its website, publicly available information reveals that Vectra’s Cognito Threat Detection and Response pricing ranges up to $5,000 for month-to-month licenses and up to $50,000 for annual licenses, depending on your selected service. For actual rates, contact Vectra’s sales team for a quote.
Features
- Automatically analyzes attacker behaviors post-compromise and in real time.
- Automatically correlates, scores, and ranks incidents by urgency across all network, identity, cloud, and SaaS environments.
- Threat intelligence integration.
- AI-based threat detection and response geared for hybrid attack defense.
- Machine learning techniques, including deep learning and neural networks.
![]()
Cybereason: Best for Defending Against MalOps
Cybereason’s platform uses behavioral analytics and artificial intelligence to detect and respond to threats in real-time, helping organizations recognize and stop attacks before they can cause significant damage.
Among its other defense strategies, Cybereason’s platform combats MalOps, which is the full range of events that take place in coordinated hacking attacks. To accomplish this, the solution uses NGAV-based behavioral and machine learning techniques, with an approach that works to prevent known and unknown MalOps threats for fast response across the network and cloud infrastructure.
Cybereason uses an AI-driven XDR platform – as cybersecurity professionals know, the XDR architecture is considered to be leading-edge in the security sector. Its XDR tools enable forensic analysis to assist security teams as they investigate and remediate security incidents in rapid-response mode.
Pros and Cons
| Pros | Cons |
|---|---|
| Automatic prediction and response to mitigate attack without human intervention. | Steep learning curve. |
| Quality customer support. | Lacks reporting capability. |
| Easy deployment. |
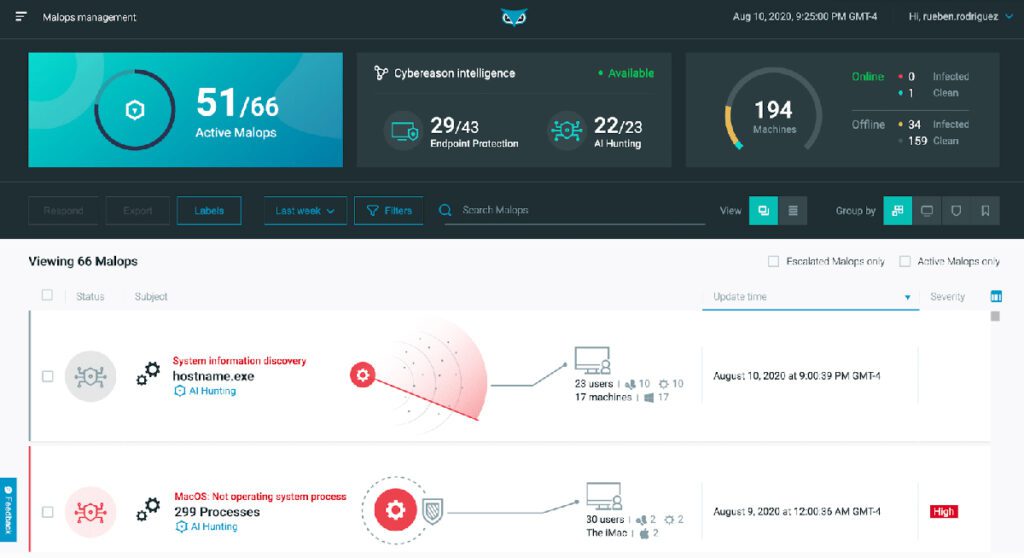
Pricing
Potential customers must contact an expert at Cybereason to receive pricing information.
Features
- Posture and incident management.
- Threat intelligence.
- Mobile threat defense.
- Digital forensic and incident response.
![]()
Tessian: Best for Protecting Against Email-Based Threats
Tessian’s platform uses AI behavior-based protection to prevent accidental and intentional loss of data over email – an important goal, given that email is one of the true weak points in the perimeter.
Tessian protects organizations from phishing attacks, accidental data leakage, and unauthorized email activity. It uses AI algorithms to analyze email communication patterns, identify suspicious behavior, and provide real-time warnings and training to employees regarding potential security risks. Significantly, Tessian is capable of protecting companies against compromised business email, account takeover and “misdirected” email. It also offers tools to combat image and QR code attacks, which is an attack type that will likely grow in the years ahead.
Tessian’s goal is to make email communication more secure and prevent data breaches caused by human error or malicious intent. The worst of these threats, like financial fraud and credential theft, do certainly deserve special tools to combat them – they cost businesses large sums annually.
Pros and Cons
| Pros | Cons |
|---|---|
| Hunt, investigate, and respond to email threats quickly. | Steep learning curve. |
| Threat network analysis. | Some users reported they experience occasional false positives. |
| Email exfiltration protection. |

Pricing
Tessian doesn’t advertise its product pricing on its website. However, publicly available data shows that the Tessian Cloud Email Security platform (100 inboxes protected) costs $40,080 per year. Contact the company sales team for a quote to get your actual pricing.
Features
- Protect against QR code phishing, BEC, executive impersonation, and domain spoofing.
- Automate removal of end user reported threats.
- Behavioral analysis.
- Tessian’s machine learning identifies threats in image-based text, QR codes, URLs, subject headings, body text, and inside of email attachments.
Honorable Mentions: Leading AI Security Solutions
Aside from the AI security solutions we analyzed above, other top-tier platforms worth mentioning are as follows.
- Cylance: A cybersecurity solution that leverages AI and ML to detect and prevent malware. Cylance AI offers protection for modern enterprise infrastructure, legacy devices and isolated endpoints.
- Deep Instinct: The company uses a prevention-first approach to stop ransomware and other malware by using predictive prevention powered by deep learning.
- LogRhythm: LogRhythm is a security intelligence company that offers various cybersecurity solutions, including SIEM, SOAR, UEBA and NDR to help organizations detect, investigate and respond to cyberattacks.
- VIPRE: VIPRE offers two threat intelligence solutions (VIPRE ThreatAnalyzer and VIPRE ThreatIQ) designed to detect, analyze and destroy persistent threats
- Stellar Cyber: Stellar is an AI-driven open XDR platform that collects and normalizes security alerts, logs and telemetry from products. It also automatically detects and correlates threats using purpose-built Graph ML, allowing you to hunt for, investigate and eliminate threats quickly.
- Sophos: The company offers detection and response, firewall, cloud and managed service solutions for network security and unified threat management.
- Dataminr: Dataminr offers real-time event and risk detection to help you discover, prioritize and categorize critical information. They use deep learning-based multi-modal AI fusion methods to improve event detection accuracy.
- Cynet: The solution offers an automated XDR platform that allows security teams to detect, prevent, correlate, investigate and respond to threats across endpoints, users, networks and SaaS applications.
- SparkCognition: SparkCognition offers AI solutions that enable companies to predict future outcomes, optimize processes and prevent cyberattacks.
- Targeted Attack Analytics (TAA) by Symantec: TAA identifies incidents with AI and advanced machine learning. Symantec EDR uses TAA data to generate new incidents or to add to existing Symantec EDR incidents.
How to Choose the Best AI-Based Security Tools for Your Business
Many factors determine the best AI security solution for you. These include your security needs, organization size, team, and budget. While most AI security software promises similar capabilities, they are not created equal — some are more powerful than others, with cutting-edge XDR capability, while some excel in certain areas like predictive threat response.
For instance, Tessian caters to those shopping for email security, while Check Point is more focused on network security. Vectra includes tools to prevent hybrid attacks.
Review your current security architecture and determine which areas need AI-powered solutions — email security, network security, endpoint protection, data loss prevention, or insider threat detection. Be sure to consider costs, features, complexity, and integrations before settling for a solution. To the extent possible, use a trial version of the AI cybersecurity solution before making a final decision.
Frequently Asked Questions (FAQs)
We answered the most commonly asked questions about the best AI security solutions to help you determine the best option for your business.
What is the best AI security solution?
The best AI security tool for you depends on your needs. Our analysis above evaluated several top-rated AI security solutions for different users. The best solution for your business is one that integrates fully into your existing infrastructure.
How do AI security solutions detect and prevent threats?
AI security solutions leverage machine learning algorithms to analyze network traffic, user behavior, and system logs to detect patterns and anomalies associated with known or unknown threats. AI can analyze these threats far faster than human security administrators.
How does AI help in incident response?
AI helps in incident response by automating the analysis of security events, prioritizing alerts based on risk, and providing insights into the root cause of incidents. AI’s strength in incident response is that the system “learns” over time, and so is increasingly effective month after month.
Bottom Line: AI-Based Cyber Security Solutions
When shopping for your company’s best AI-based cyber security solution, select the one that ticks all or most of your boxes – specifically, the one that truly works with your infrastructure, with its mix of on-premise, network configuration, and cloud-based software.
As you consider the features and capabilities of various, it is also necessary to consider the product costs. Since most vendors do not advertise their rates on their website, you must contact their sales team for personalized quotes to determine if the tool is within your budget – realize you likely have some bargaining power in these situations. Additionally, ensure you understand the vendor’s reputation, customer support, and implementation process.
According to Research: AI-Based Cyber Security Tools
In the realm of cyber security, staying ahead of online threats is a constant challenge. With the proliferation of cyber attacks becoming increasingly sophisticated, organizations and individuals alike are seeking innovative solutions to protect their digital assets. Recent research on AI-based cyber security tools sheds light on the effectiveness of leveraging artificial intelligence (AI) in fortifying cyber defenses. Let’s delve into the findings and discover the top AI-based cyber security tools that are making waves in the industry.
Research Insights
1. Enhanced Threat Detection
Research indicates that AI-based cyber security tools excel in threat detection capabilities. By analyzing vast amounts of data and patterns, these tools can identify anomalies and suspicious activities with high precision, enabling organizations to preemptively thwart cyber attacks before they wreak havoc.
2. Real-Time Response
One of the key advantages of AI-powered cyber security tools is their ability to provide real-time response to emerging threats. Through machine learning algorithms, these tools can autonomously adapt and evolve their defense mechanisms, ensuring swift and effective mitigation of cyber risks.
3. Proactive Defense
Research underscores the importance of proactive defense in the face of cyber threats, and AI-based tools are leading the charge in this regard. By leveraging predictive analytics and behavioral analysis, these tools can anticipate cyber attacks and proactively implement countermeasures to safeguard critical assets.
If you want to learn about A.I. Artificial Intelligence Click here




